A highly strange botnet was found which has spellbound more than 12,000 computer systems while disguising itself as an authentic add-on for the famous Mozilla Firefox internet browser. The botnet forces the computers it gets on to analyze websites for their flaws in security.
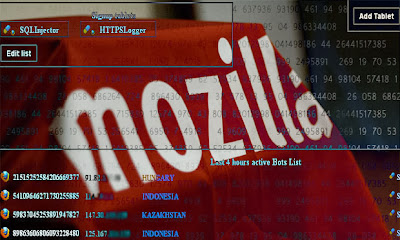
This highly dangerous botnet, called “Advanced Power” by its developers, seems to have been into existence since May 2013 or even before that. Nobody is able to explain how the malware program is being spread to infect these many computers. It works in a way where it enslaves its victim PCs in a botnet and carries out SQLInjection attacks on any website that the victim visits.
The more serious property of this dark botnet is to extract passwords and other personal and sensitive information from the machines it has infected, but you may take a silent deep breath as this feature doesn’t appear to be in function on these infected hosts. Instead, this botnet is functioning only to use the slave Windows desktops as a wide scanning platform for searching for websites which can be exploited easily.
According to the Administrative Panel of Advanced Power, at least 12,500 PCs are under infection and have helped in finding at around 18,000 Web Pages which are exploitable by SQL Injection Attacks.
The code being injected in the websites is from sources from the following two links:
We wouldn’t really recommend you going out looking for this malware!
Now on the infected PCs with the Mozilla Firefox browser, the bot code installs itself as a browser plug-in, calling itself “Microsoft .NET Framework Assisstant”, which is bogus and completely different from what the original plugin is. After installing itself on Mozilla, the bot code checks every page the user visits from the browser and tests them for any SQL Injection exploitability.
Hold Security LLC’s chief information security officer, Alex Holdencommented that the botnet program seems to have been developed to automate the hectic blind guesswork which gets involved in probing websites for SQL Injection Attacks vulnerabilities. Holden added to his comment that when testing of an application for SQL injection or any other vulnerability has to be performed, there is a small frame of reference as to the site’s functionality. Adding what he quoted, “You often don’t know or can’t see many user functions. And in some cases you need proper credentials to do it right. In this case, the hackers are using valid requests within many sites that end-users themselves are feeding them. This is a much bigger sample than you would normally get. By no means is it a full regression test, but it is a deep and innovative approach.”
Holden believes that the developers of Advanced Power are from the Czech Republic, as he noted that a few transliterated strings of text in the malware are auto-detected as Czech by Google Translate language program from Google.
Advanced Power is a solid example of how today’s infected systems are regularly used to take shots at destroying the defense systems guarding privacy and information of other users online. What makes the story more interesting is that there exists an Add-On for Firefox that runs the same test on the websites a user visits, but for reasons of testing security. Readers who are looking for a free tool to test their sites’ strength against such attacks should try using SQLmap which is an open source testing tool for penetration attacks like the SQL Injection itself.
Mozilla has recently issued a comment on the same, “We have disabled the fraudulent Microsoft .NET Framework Assistant add-on used by Advanced Power botnet,” by adding the fraudulent add-on to its blocked list. According to Mozilla, Firefox displays a message everyday once as it checks for blocked add-ons, while the browser is being used, and the blocking doesn’t require the user to take any actions to be in effect.
No comments:
Post a Comment