
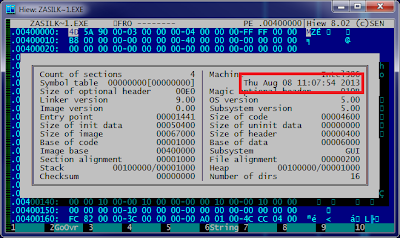
Speaking about the issue at RSA Conference Europe 2013 in Amsterdam, researchers have provided details on this vulnerability, which stems from a commonly used approach to URL caching.
Demonstration shows that insecure public networks can also provide stealth access to our iOS apps to potential attackers using HTTP request hijacking methods.
Demonstration shows that insecure public networks can also provide stealth access to our iOS apps to potential attackers using HTTP request hijacking methods.
The researchers put together a short video demonstrating, in which they use what is called a 301 directive to redirect the traffic flow from an app to an app maker’s server to the attacker’s server.
There are two limitations also, that the attacker needs to be physically near the victim for the initial poisoning to perform this attack and the flaw works only against HTTP traffic.
“A victim walks into Starbucks, connects to the Wi-Fi and uses her favorite apps,” explains an example. “Everything looks and behaves as normal, however an attacker is sitting at a nearby table and performs a silent HRH attack on her apps. The next day, she wakes up at home and logs in to read the news, but she’s now reading the attacker’s news!”
They estimate that at least 10,000 iOS apps in the Apple App Store are vulnerable to the hack. As a result, apps that display news, stock quotes, social media content, or even some online banking details can be manipulated to display fraudulent information and intercept data sent by the end user.
Victims can uninstall apps to scrub their devices clean, and Skycure has released app code that prevents the web caching from taking place. It may be a while until developers can get this fix implemented, so connect to those public networks with extreme caution.













.jpg)


.jpg)
.jpg)
.jpg)



